DECEMBER 2006
Code: A-28 Subject: COMPUTER NETWORKS
Time: 3 Hours Max. Marks: 100
NOTE: There are 9 Questions in all.
· Question 1 is compulsory and carries 20 marks. Answer to Q. 1. must be written in the space provided for it in the answer book supplied and nowhere else.
· Out of the remaining EIGHT Questions answer any FIVE Questions. Each question carries 16 marks.
· Any required data not explicitly given, may be suitably assumed and stated.
Q.1 Choose the correct or best alternative in the following: (2x10)
a. The main function of the transport layer is
(A) node-to-node delivery (B) process-to-process delivery
(C) synchronization (D) updating and maintenance of
routing tables.
b. A telephone network is an example of a ___________ network.
(A) Packet-switched (B) Circuit-switched
(C) Message-switched (D) None of these
c. Flow control is needed to prevent_________.
(A) Bit errors (B) Overflow of the sender buffer
(C) Overflow of the receiver buffer (D) Collision between sender and receiver
d. ________ is the access protocol used by IEEE 802.11.
(A) CSMA (B) CSMA / CD
(C) CSMA / CA (D) Token ring
e. A FHSS wireless LAN has a spread spectrum of 1GHz. If the bandwidth of the original signal is 250 MHz, there would be ___________ hops per cycle.
(A) 1 (B) 2
(C) 3 (D) 4
f. Bridges function in the ________ layers.
(A) MAC (B) Data link
(C) Network (D) Both (A) and (B)
g. An IPV6 address consists of _______ bits.
(A) 4 (B) 8
(C) 32 (D) 128
h. Internet Telephony and Video conferencing uses the following protocol.
(A) RTP (B) UDP
(C) TCP (D) HTTP
i. A cipher refers to
(A) An encryption algorithm (B) A decryption algorithm
(C) A private key (D) Both (A) & (B)
j. The maximum segment length in a 10BASE F Ethernet system is
(A) 500 m (B) 200 m
(C) 100 m (D) 2 km
Answer any FIVE Questions out of EIGHT Questions.
Each question carries 16 marks.
Q.2 a. Differentiate between
(i) Confirmed and unconfirmed service.
(ii) Connectionless and connection-oriented service.
(iii) PDU and SDU. (6)
b. Discuss the communication through the socket interfaces with a suitable schematic diagram. (6)
c. For 10 devices in a network, what is the number of cable links needed for a mesh ring and star topology? (4)
Q.3 a. Describe a synchronous TDM transmitter system with block schematics. (6)
b. In stop and wait ARQ, why should the receiver always send an ACK message each time it receives a frame with the wrong sequence number? (5)
c. Frames of 10,000 bits
are sent over 2Mbps satellite channel. What is the maximum achievable channel
utilisation for stop and wait protocol? Ignore the time required for error
detection and assume ![]() . (5)
. (5)
Q.4 a. Explain the basic requirements of ARQ with a diagram. (6)
b. Discuss FDDI frame structure. (6)
c. Differentiate between transparent and source routing bridges. (4)
Q.5 a. Why is packet switching preferred to circuit switching in computer networks? Compare message switching with packet switching showing delays in the operation. (2+6)
b. Draw the format of TCP segment and briefly explain the function of each field. (8)
Q.6 a. A TCP connection with 65,535 bytes windows is sent over 1 Gbps channel. The channel has a round trip delay of 20 m secs.
Find
(i) The maximum achievable throughput.
(ii) Line efficiency. (6)
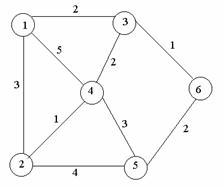
b. For the network shown below, use the Dijkstra’s algorithm to find the set of shortest paths from node 4 to other nodes. Also find the set of associated routing table entries. (6)
|
c. Identify the address of the following IP addresses:
(i) 200.58.20.165 (ii) 128.167.23.20
(iii) 16.196.128.50 (iv) 150.156.10.10 (4)
Q.7 a. Draw the UDP header format and mention its advantage over TCP. (6)
b. Discuss PNNI routing with an example. (6)
c. How are attacks on network security categorised? (4)
Q.8 a. How is public key encryption useful in message authentication and key distribution? Explain with a scheme. (8)
b. Give example of HTTP operation with suitable diagrams. (8)
Q.9 Write explanatory note on any TWO of the following:
(i) RSVP
(ii) 802.11 standard
(iii) Queuing Models (2 x 8=16)